PassLeader now are offering 100% pass ensure 1Z0-052 dumps! All 1Z0-052 exam questions have been updated with correct answers, welcome to download the newest PassLeader 1Z0-052 VCE dumps and PDF dumps: http://www.passleader.com/1z0-052.html (261 Q&As)
BTW: Download PassLeader 1Z0-052 dumps from Google Drive for free: https://drive.google.com/open?id=0B-ob6L_QjGLpaXlIQVBWWmRoa1U
QUESTION 121
Your database instance is functional for the past one month. The Automatic Workload Repository (AWR) snapshot retention is set to 7 and the STATISTICS_LEVEL initialization parameter is set to TYPICAL. You receive a complaint about the poor performance of the database between 7 PM and 9 PM of the previous day. Choose two actions any of which can be referred to first to diagnose the problem. (Choose two.)
A. Use the Active Session History report.
B. Use the AWR Compare Periods report.
C. Use an ADDM analysis between 7 PM and 9 PM of the previous day.
D. Use the AWR Compare Period report between 7 PM and 9 PM of the previous day.
Answer: BC
QUESTION 122
Which two statements are true about the Automatic Workload Repository (AWR)? (Choose two.)
A. All AWR tables belong to the SYSTEM schema
B. The AWR contains systemwide tracing and logging information
C. The snapshots collected by the AWR are accessible through data dictionary views
D. The snapshots collected by the AWR are used by self-tuning components in the database
Answer: CD
QUESTION 123
View the Exhibit and examine the PL/SQL package and procedure. You made changes to the COMPUTE_TAX function inside the EMP_ADMIN package body. Which statement is true after you recompile the EMP_ADMIN package body?
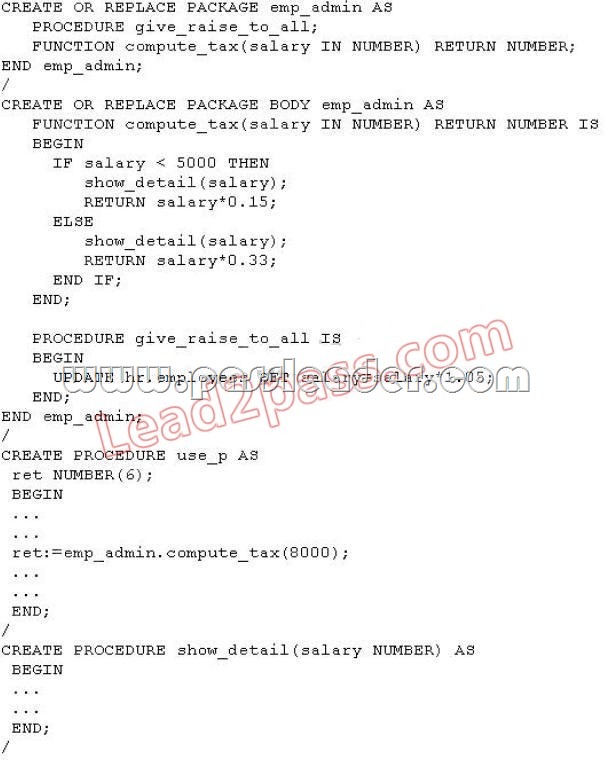
A. The USE_P procedure remains valid.
B. The USE_P procedure becomes invalid.
C. The SHOW_DETAIL procedure becomes invalid.
D. The EMP_ADMIN package specification becomes invalid and needs to be recompiled.
Answer: A
QUESTION 124
View the Exhibit. What would happen if Oracle Home is not empty?
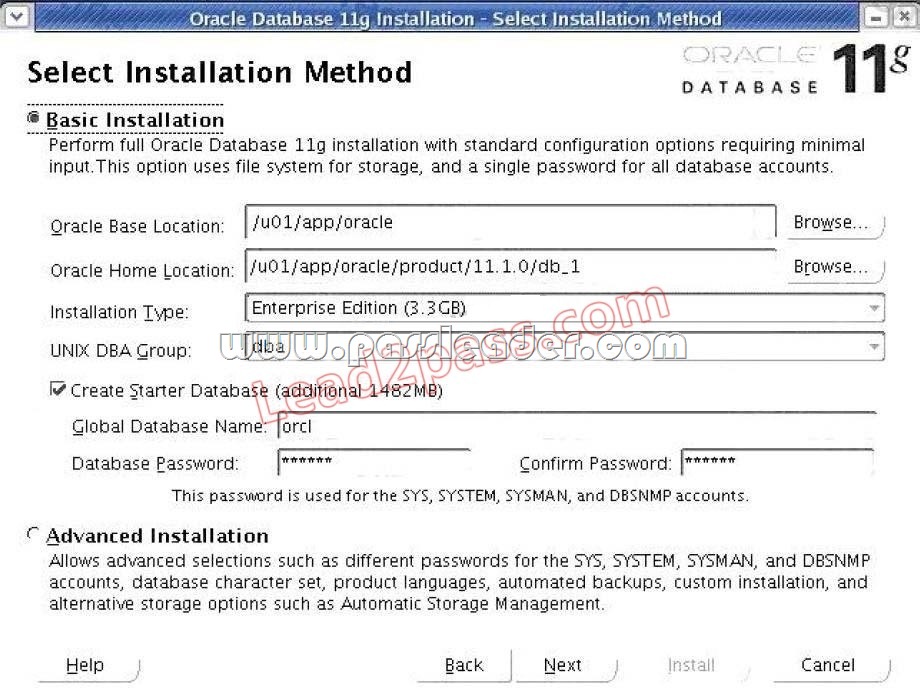
A. The installation will not be continued until the location is empty.
B. The installation will proceed without overwriting the existing files.
C. The installation can be continued, but the existing files will be overwritten.
D. The installation terminates automatically after showing an error message.
Answer: A
QUESTION 125
Identify three situations in which you would NOT be able to drop a tablespace. (Choose three.)
A. when the tablespace is online
B. when the tablespace has segments with data in it
C. when the tablespace is a default permanent tablespace for the database
D. when the tablespace contains a table that is currently being used by transactions
E. when the tablespace contains undo data that is needed to rollback an uncommitted transaction
Answer: CDE
QUESTION 126
The user SCOTT owns the CUST table that is placed in the SALES tablespace. The user SCOTT opens a session and executes commands as follows:
SQL> INSERT INTO cust VALUES(101, ‘JACK’);
1 row created.
SQL> INSERT INTO cust VALUES(102, ‘SMITH’);
1 row created.
As a DBA, you execute the following command from another session:
ALTER TABLESPACE sales READ ONLY;
Which statement is true regarding the effect of this command on the transaction in Scott’s session?
A. The command fails as a transaction is still pending.
B. The transaction in Scott’s session is rolled back and the tablespace becomes readonly.
C. The command waits and the user SCOTT can execute data manipulation language (DML) statements only as part of the current transaction.
D. The command hangs until all transactions on the objects in the tablespace commit or rollback, and then the tablespace is placed in readonly mode.
Answer: D
QUESTION 127
You plan to configure the new Oracle Database 11g installation by performing these tasks:
– Use Automatic Storage Management (ASM) as the storage option.
– Use Oracle Enterprise Manager Database Control to manage the database.
– Provide the same password for SYS, SYSTEM, SYSMAN, and DBSNMP accounts during the installation.
– Configure the database to send email notifications.
Some tools available to you for installation are:
1: Oracle Universal Installer (OUI)
2: Database Configuration Assistant (DBCA)
3: Database Upgrade Assistant (DBUA)
4: Oracle Net Configuration Assistant
Which tools would you use for this installation?
A. 2
B. 3
C. 1 and 2
D. 3 and 4
E. 1,2 and 4
Answer: E
QUESTION 128
Which three descriptions are correct about the effects of the TRUNCATE command on a table? (Choose three.)
A. The corresponding indexes for the table are also truncated.
B. Delete triggers on the table are fired during the execution of the TRUNCATE command.
C. The child table is truncated when the TRUNCATE command is applied on the parent table.
D. The highwater mark (HWM) is set to point to the first usable data block in the table segment.
E. No undo or very little undo data is generated during the execution of the TRUNCATE command.
Answer: ADE
QUESTION 129
The tnsnames.ora file has an entry for the service alias ORCL as follows:
ORCL =
( DESCRIPTION =
(ADDRESS = (PROTOCOL = TCP)(HOST = 10.156.24.216)(PORT = 1521))
(CONNECT_DATA =
(SERVER = DEDICATED)
(SERVICE_NAME = orcl.oracle.com)
)
)
The TNSPING command executes successfully when tested with ORCL, but you are not able to connect to the database instance with the following command:
SQL> CONNECT scott/tiger@orcl
What could be the reason for this?
A. The listener is not running on the database node.
B. The TNS_ADMIN environmental variable is set to a wrong value.
C. The orcl.oracle.com database service is not registered with the listener.
D. The DEFAULT_DOMAIN parameter is set to a wrong value in the sqlnet.ora file.
Answer: C
QUESTION 130
You suspect unauthorized data manipulation language (DML) operations on a particular table. You want to track users who are performing the transactions and the values used in the transactions. You also plan to transfer these values to another table for analysis. How would you achieve this?
A. by using triggers
B. by using Data Pump
C. by using external tables
D. by using anonymous PL/SQL blocks
Answer: A
QUESTION 131
You execute a command to resize a data file, sales.dbf, of size 200 MB in your database:
ALTER DATABASE DATAFILE ‘/remorse/sales.dbf’ RESIZE 150M;
Which statement is true about this command?
A. The command must be issued in MOUNT state.
B. The command succeeds only if the data file is offline.
C. The command must be issued when the database is in the archivelog mode.
D. The command succeeds if no extent in the tablespace is currently allocated above the 150 MB boundary of the file.
Answer: D
QUESTION 132
You executed the following commands to find the location of the alert log file:
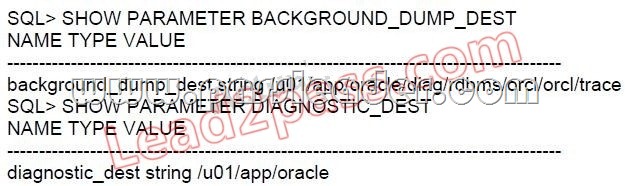
Where is the alert log file stored? (Choose all that apply.)
A. in the BACKGROUND_DUMP_DEST location; in text format
B. in the BACKGROUND_DUMP_DEST location; in XML format
C. in the BACKGROUND_DUMP_DEST location; in both text and XML format
D. in the DIAGNOSTIC_DEST/diag/rdbms/orcl/orcl/alert directory; in text format
E. in the DIAGNOSTIC_DEST/diag/rdbms/orcl/orcl/alert directory; in XML format
F. in the DIAGNOSTIC_DEST/diag/rdbms/orcl/orcl/alert directory; in both text and XML format
Answer: AE
QUESTION 133
You created a profile APP_USER and assigned it to the users. After a month, you decide to drop the profile. Some user sessions are currently connected to the database instance and are using the APP_USER profile. This command is used to drop the profile:
SQL> DROP PROFILE app_user;
Which statement describes the result?
A. The command produces an error.
B. The profile is dropped and current user sessions use the DEFAULT profile immediately.
C. The profile is dropped and only the subsequent user sessions use the DEFAULT profile.
D. The profile is dropped, the sessions are terminated, and the subsequent user sessions use the DEFAULT profile.
Answer: A
QUESTION 134
View the Exhibits and examine lock waits. Users HR and SH complain that their transactions on one of the application tables, EMP, are waiting for response. Which action would you take to release the lock and enable users HR and SH to continue with their transactions?

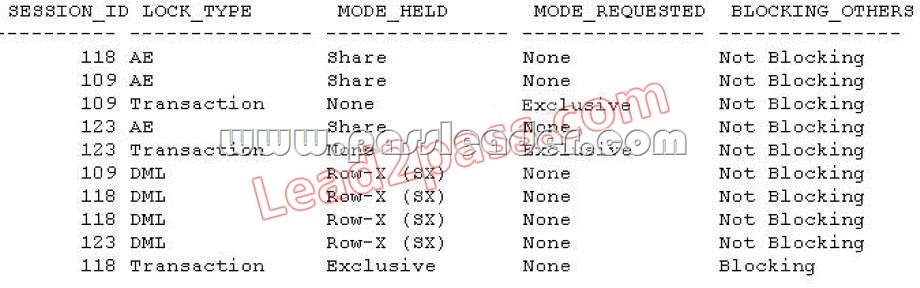
A. Kill the session of the user SCOTT with session ID118.
B. Issue manual checkpoint using the ALTER SYSTEM command.
C. Modify the profile used by user SCOTT to reduce the CONNECT_TIME limit.
D. Flush the Shared Pool to remove the SQL statement causing “wait” in memory.
Answer: A
QUESTION 135
Note the functionalities of various background processes:
1: Perform recovery at instance startup.
2: Free the resources used by a user process when it fails.
3: Cleanup the database buffer cache when a process fails.
4: Dynamically register database services with listeners.
5: Monitor sessions for idle session timeout.
6: Cleanup unused temporary segments.
7: Record the checkpoint information in control file.
Which option has the correct functionalities listed for a background process?
A. Checkpoint (CKPT): 1, 2, 5
B. System Monitor (SMON): 1, 6
C. Process Monitor (PMON): 4, 6, 7
D. Database Writer (DBWR): 1, 3, 4
Answer: B
QUESTION 136
Identify the logical structure that will never have more than one data segment created for it.
A. external table
B. partitioned table
C. partitioned index
D. nonclustered table
E. global temporary table
Answer: D
QUESTION 137
View the Exhibit and examine the command used to create the ZONEDATA table. The table contains a million rows for zonewise analysis in the DSS system. DML operations are performed very rarely on the table. You decide to prepare an index on the ZONE column to enhance the performance of the queries on the ZONE column. Which type of index would you select in this scenario?
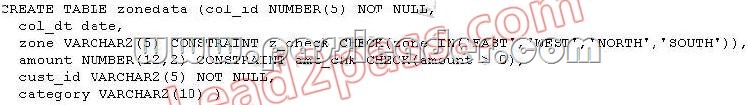
A. Bitmap index
B. Reverse key index
C. Normal BTree index
D. Functionbased index
Answer: A
QUESTION 138
The user HR owns the EMP table. The user HR grants privileges to the user SCOTT by using this command:
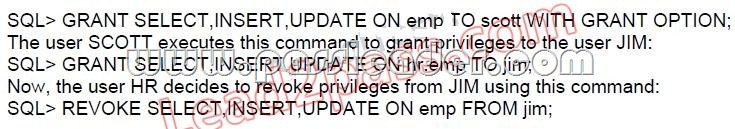
Which statement is true after HR issues the REVOKE command?
A. The command fails because SCOTT still has privileges.
B. The command succeeds and privileges are revoked from JIM.
C. The command fails because HR cannot revoke the privileges from JIM.
D. The command succeeds and only HR has the privilege to perform the SELECT, INSERT, and UPDATE operations on the EMP table.
Answer: C
QUESTION 139
Which statement describes the effect on an index, when the indexed column for the rows is updated in the base table?
A. An update in a leaf row takes place.
B. The index becomes invalid after the update.
C. The leaf block containing the row to be updated is marked as invalid.
D. A row in the leaf block of the index for the key value is logically deleted and a new leaf row is inserted.
Answer: D
QUESTION 140
You are managing an Oracle Database 11g database running in ARCHIVELOG mode. The Flash Recovery Area is specified as the destination for the archived redo log files. You notice this warning in the alert log file:
ORA19815: WARNING: db_recovery_file_dest_size of 3221225472 bytes is 100.00% used, and has 0 remaining bytes available.
What would you do to reclaim the used space in the Flash Recovery Area? (Choose two.)
A. Back up the Flash Recovery Area.
B. Decrease the retention time for the database backup and flashback log files.
C. Manually delete all the archived log files from the Flash Recovery Area by using operating system (OS) commands.
D. Manually delete all the expired backup sets from the Flash Recovery Area by using operating system (OS) commands.
Answer: AB
PassLeader now are offering 100% pass ensure 1Z0-052 dumps! All 1Z0-052 exam questions have been updated with correct answers, welcome to download the newest PassLeader 1Z0-052 VCE dumps and PDF dumps: http://www.passleader.com/1z0-052.html (261 Q&As)
BTW: Download PassLeader 1Z0-052 dumps from Google Drive for free: https://drive.google.com/open?id=0B-ob6L_QjGLpaXlIQVBWWmRoa1U